Forescout Technologies – A Leader in NAC Technology for Authentication, Access Control, and Centralized IoT Protection
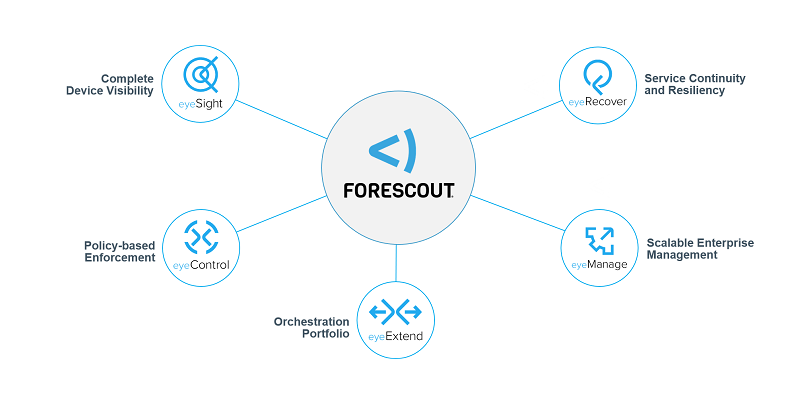
ForeScout: Centrally Monitor and Control All Devices Across the Network ForeScout CounterACT has evolved from a Network Access Control (NAC) system—consistently recognized as a Leader in Gartner’s Magic Quadrant—into a comprehensive security solution designed to protect devices across enterprise networks. It offers a wide range of capabilities to address diverse security needs, including:
1. Discover and classify all devices on the network with real-time inventory Once ForeScout CounterACT is deployed and initially configured, it immediately scans the network to identify all connected devices, including their MAC addresses, IP addresses, device types, operating systems, active services, associated users, and more. This information is compiled into a real-time inventory, enabling administrators to instantly gain full visibility of all devices and their locations within the network. This insight supports better policy design and network security management.
Because this real-time inventory does not require installing software agents on endpoints, ForeScout can detect and analyze any device connected to the network—as long as it has a MAC or IP address.
2. Authenticate and enforce access control for all devices, including BYOD and IoT With agentless device visibility, ForeScout can verify authentication status across all devices—whether through its own web portal, 802.1X authentication, Microsoft Active Directory login, or other methods.
Since ForeScout can identify both authentication status and device type, organizations can design flexible authentication workflows, such as:
Devices authenticated via 802.1X or Microsoft AD can access the network based on predefined policies without additional portal authentication Unauthenticated devices must authenticate via a web portal and may receive different access levels Users without credentials can register for temporary network access All authentication activities (successful or failed) are automatically logged These workflows can be customized further with conditions such as OS type, endpoint security compliance, and device category—allowing tailored network access policies.
3. Deep visibility and control at the application, security, and hardware levels ForeScout enables deep management of Windows, Linux, and macOS endpoints through integration with Microsoft Active Directory and lightweight agents. Administrators can monitor system resources (CPU, RAM, disk), running applications and services, installed software, patch status, USB connections, and more.
Additionally, ForeScout allows administrators to control endpoints by executing scripts, installing or removing software, sending user alerts, and triggering antivirus scans—ensuring secure device usage across the network.
4. Automatically detect and mitigate network attacks With built-in traffic monitoring, ForeScout can identify suspicious activities such as network scanning attempts, abnormal port access, excessive email traffic, and more. It can detect threats that other security systems may miss and respond in real time to prevent potential attacks.
5. Integrate with other security systems to enable Software-Defined Security ForeScout’s ControlFabric architecture allows it to act as a central integration point for network and security events. It collects and analyzes data from various systems to identify compromised or non-compliant devices and orchestrates responses either directly or through other systems, such as:
Monitoring login/logout events from switches, wireless controllers, VPNs, routers, etc. Aggregating security data from firewalls, IPS, vulnerability scanners, EMM, MDM, endpoint protection, and threat intelligence systems Receiving insights from SIEM and advanced threat detection tools Automating responses—for example, isolating vulnerable devices and triggering patch management systems before restoring access
6. Flexible reporting and real-time compliance across the network ForeScout enables organizations to define and monitor compliance requirements in real time across all endpoints. It continuously evaluates device status against policies and provides immediate alerts when violations occur, allowing rapid remediation.
It also includes dozens of ready-to-use reports, such as inventory reports, security reports, and trend analyses.
With these capabilities, ForeScout has received numerous industry awards and recognitions.
How is ForeScout different from a Firewall? This is a common question among organizations—especially whether ForeScout is still needed if a firewall is already in place. The answer depends on the level of security required, and can be considered as follows:
1. Can your firewall fully authenticate and control access for every user? Firewalls typically rely on static policy rules and are not designed for dynamic, user-based access control. Managing per-user access policies on a firewall can be resource-intensive.
In contrast, ForeScout is specifically designed to enforce granular, user-based security policies, making it ideal for organizations requiring flexible access control.
2. Can your organization detect internal network attacks? Most security tools focus on threats from external networks or endpoint-to-data center traffic. ForeScout enhances security by detecting lateral attacks within the network—common in advanced threats such as malware, worms, and insider attacks.
3. Does your organization have full visibility of all connected devices? With the rise of BYOD and IoT, tracking all connected devices is critical. ForeScout provides real-time inventory and visibility, enabling IT teams to manage and secure all devices effectively.
4. Can your organization easily enforce real-time compliance across all devices? As networks grow, compliance becomes more complex. ForeScout simplifies compliance by continuously monitoring and enforcing policies across all devices, even those previously unknown to IT teams.
Contact Throughwave Thailand – Official Distributor of ForeScout in Thailand Organizations interested in ForeScout network security solutions or related technologies such as Mobile Device Management, Network Security, Firewall, SSL-VPN, and more can contact Throughwave Thailand for consultation, recommendations, or quotations at info@throughwave.co.th or call 02-210-0969. Visit https://www.throughwave.co.th/ for more information.
Learn More About ForeScout CounterACT In-depth: Real-time monitoring of users and devices In-depth (Part 2): Protecting networks from cyber threats In-depth (Part 3): Centralized endpoint management In-depth (Part 4): Securing BYOD and mobile devices Best practices for BYOD security with Network Access Control Explore more about ForeScout CounterACT:
https://www.throughwave.co.th/2020/08/17/forescout-add-new-features-support-enterprise-of-things/